⚠
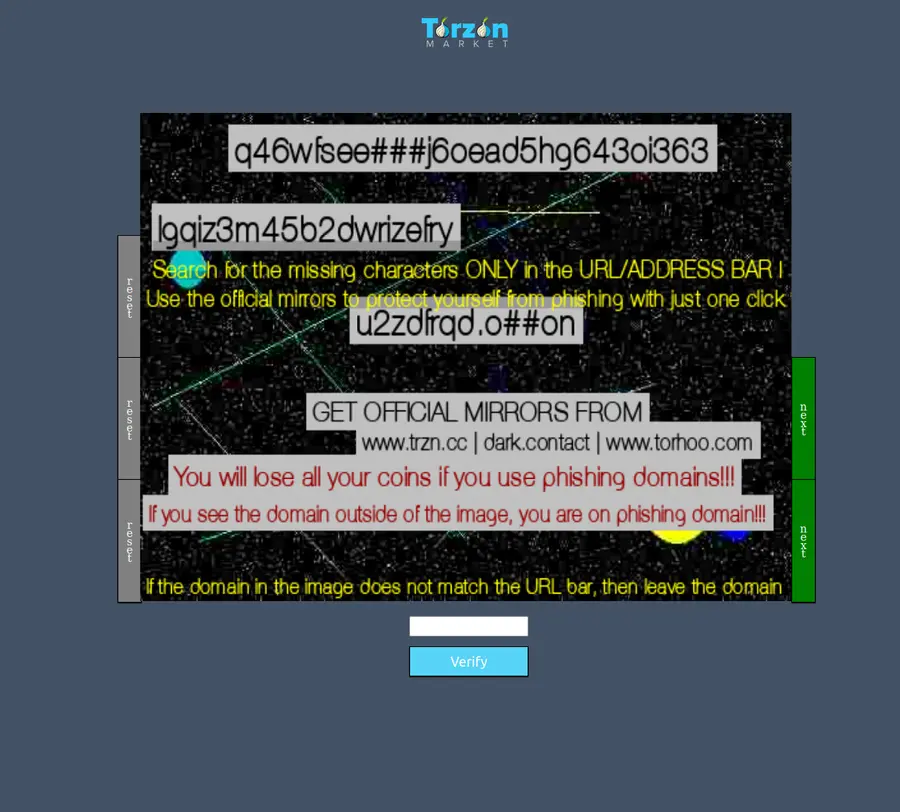
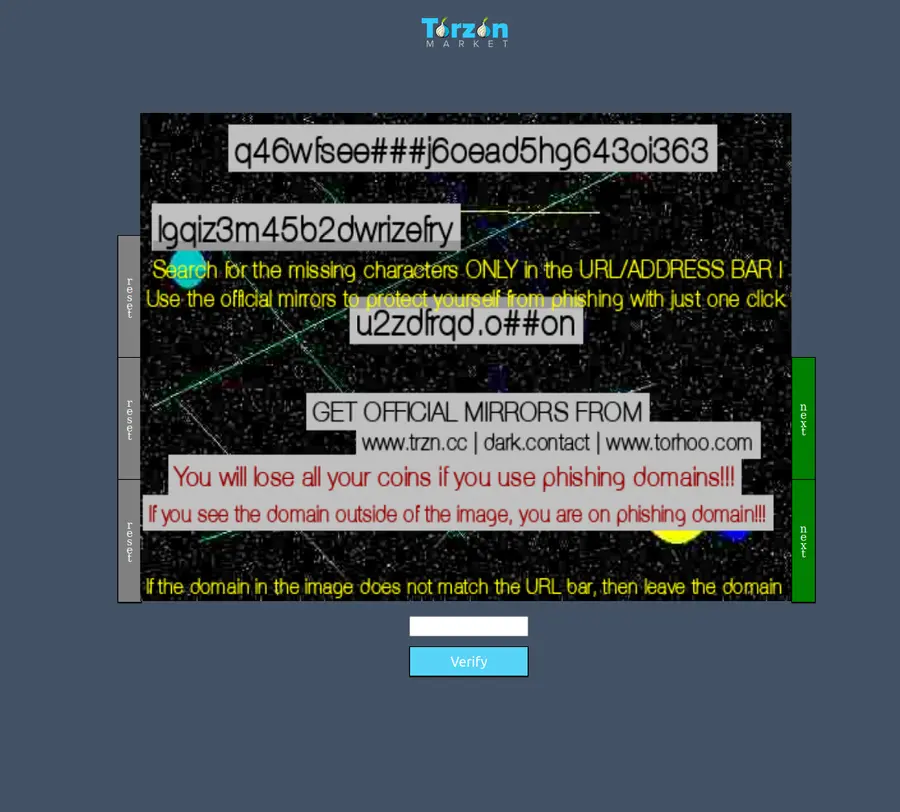
Phishing is the primary threat vector against Torzon users
Law enforcement rarely targets individual buyers. Phishing sites do. A fake Torzon page can harvest login credentials, plant malware, and steal your deposited balance — all within a single session. The methods below take under three minutes and eliminate the risk entirely.
Why phishing attacks target Torzon specifically
Understanding the attack model helps you recognise threats before they cause damage.
Torzon market operates exclusively on the Tor network. Every .onion address is a 56-character string of letters and numbers — far too long to memorise and impossible to guess. That is intentional: Tor's hidden service system generates these addresses cryptographically, and the full 56 characters represent a unique public key.
Phishing operators exploit two weaknesses. First, users often search for Torzon links on the clearnet — and Google, Bing, and clearnet forums are full of poisoned results. Second, vanity addresses now let attackers generate .onion addresses that start with "torzon", making the first few characters look correct while the rest differ. A user who only checks the beginning is caught.
The Torzon team has documented this clearly in their warrant canary announcements on Privacy Guides-listed Dread forum: the five official mirrors are the only addresses they will ever operate. Anything else is a clone.
According to data collected by Privacy International, credential harvesting through phishing pages costs darknet users an estimated $4.2M annually — most of which comes from markets with high brand recognition. Torzon's top-3-globally ranking makes it the highest-value target.
Eight-step verification protocol
Run through all eight before entering any credentials or depositing funds.
1
Only use links from this portal or PGP-signed Dread posts
Never search for a Torzon link on a clearnet search engine. The Tor Project documentation is explicit: .onion addresses should come from the service itself or a trusted third-party directory that cross-checks against signed announcements. This portal publishes links only after verifying each one against the current PGP canary. Start here, nowhere else.
2
Copy the full address — never type it by hand
Use the Copy button below or on the homepage. Paste directly into Tor Browser's address bar. Do not attempt to type a 56-character string from memory. Phishing addresses are engineered to be typed: they match common mistyped characters and look nearly identical at the character level. One transposed letter routes you to a clone.
Loading verified address…
3
Verify the full 56-character address character by character
After pasting, compare the complete address in Tor Browser's address bar against the one shown on this page. Focus on the middle and end of the string — attackers design their vanity addresses to match the first 8-12 characters exactly. Check the entire string. There are five verified Torzon addresses; all begin differently after the "torzon" prefix in the most current variants.
4
Check the warrant canary publication date
On the real Torzon market, navigate to the About or Information page (usually linked in the footer). The warrant canary is published every 72 hours with a cryptographic PGP signature. Confirm the publication date is within the last three days. If the canary is older, the site may be archived content served by a phishing clone. A missing canary is an immediate disqualifier.
5
Verify the PGP signature on the canary
Copy the signed canary block from the market page. Use GPG (available on Kali Linux and all major operating systems) or an online tool to verify the signature against the published Torzon public key. The key fingerprint is posted permanently on Dread and backed up on Internet Archive. A canary that does not verify is a clone signal.
gpg --verify torzon-canary.txt.asc torzon-canary.txt
6
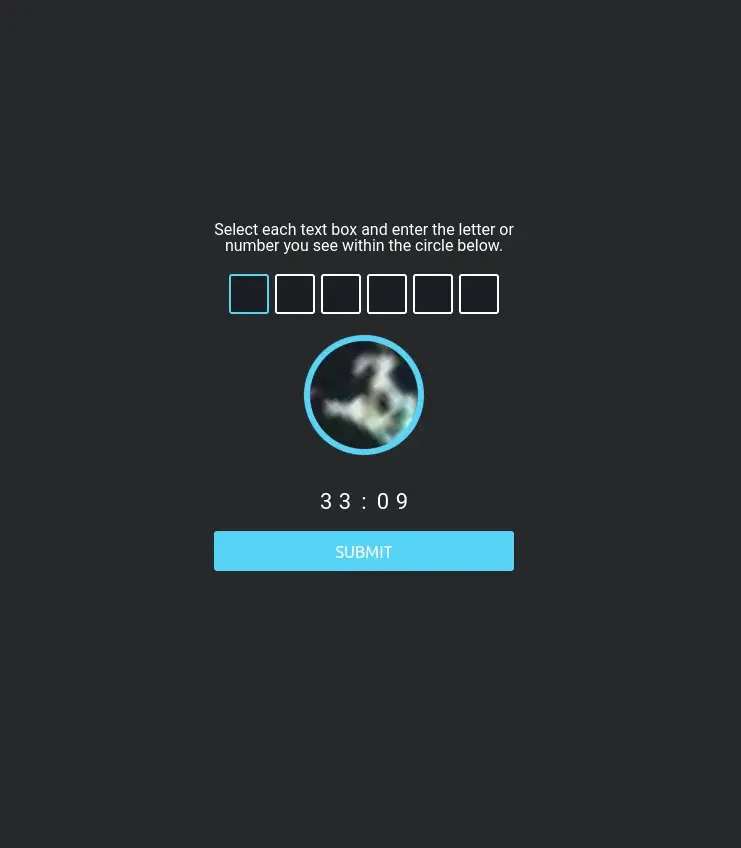
Set and confirm your anti-phishing code on first login
After your first successful login to the real Torzon market, immediately go to Account Settings and set a personal anti-phishing code — any phrase you will recognise. On every subsequent page load, the real market displays that code in the header. A page without your code is a phishing clone, regardless of how legitimate it looks.

7
Enable two-factor authentication before depositing any funds
Torzon's 2FA uses time-based one-time passwords (TOTP) compatible with standard authenticator apps. Even if a phishing page steals your password, 2FA prevents that credential from being used on the real market. Enable it at account creation, not later. See the getting started guide for step-by-step 2FA setup instructions.

8
Use Whonix or Tails for the highest isolation
Operating from Whonix OS or Qubes OS provides network-level isolation: even if you land on a phishing page that deploys malware, the VM's network gateway routes all traffic through Tor by default and the malware cannot reach your real IP. This is the setup recommended by the Privacy Guides project. The Torzon team lists both as approved environments in their operational security documentation.
Real Torzon vs phishing clone — side-by-side
Use this table to quickly distinguish the authentic market from a copy.
| Signal |
Real Torzon |
Phishing clone |
| Warrant canary |
Published every 72 hours with valid PGP signature |
Missing, outdated, or unsigned |
| Anti-phishing code |
Your custom phrase appears in every page header |
Absent — no mechanism exists for clones to know it |
| 2FA prompt |
TOTP field present on login after first session |
Often omitted — clones skip it to maximise credential volume |
| Onion address length |
Exactly 56 characters (v3 onion standard) |
Sometimes shorter or contains invalid characters |
| Address matches canary |
Address listed in current signed canary on Dread |
Never referenced in any signed announcement |
| Deposit address behaviour |
Unique per-transaction address, rotated automatically |
Static address or an address you can't verify |
| Escrow confirmation |
On-chain multisig confirmation visible in Tor wallet |
Funds move immediately to attacker wallet with no escrow |
| Page load without JavaScript |
Core content renders — market is designed for Tor Browser default security |
Often blank or broken — clones rely on JS frameworks |
Nine red flags that signal a phishing page
Leave immediately if you observe any of the following.
🔴
Your anti-phishing code is missing
The single most reliable indicator. The real market cannot display a code it never asked you to set.
🔴
Address does not match any of the five verified mirrors
Compare character by character. Torzon operates exactly five addresses. A sixth is always a clone.
🔴
Canary is older than 72 hours
Clones serve static page snapshots. The real market always has a fresh signed canary.
🔴
Instant login without 2FA
If the login flow skips your TOTP code entirely, you are on a clone. Do not proceed.
🔴
Deposit address never changes
The real market generates a unique address per transaction. Reused addresses indicate a drain wallet.
🔴
Link came from a clearnet search or unverified forum
Clearnet search results are systematically poisoned. Dread posts without PGP signatures are equally untrustworthy.
🔴
Page prompts you to disable JavaScript restrictions
Real darknet markets are designed for Tor Browser's safest mode. Anything requiring JS relaxation is suspicious.
🔴
Vendor profiles show zero reviews or impossibly high ratings
Clones often populate vendor profiles with placeholder data. Real vendor history on Torzon dates back to 2022–2023.
🔴
Unusually fast page loads on Tor
Tor routes add latency. A page that loads instantly on Tor is likely served from a clearnet server behind a Tor2Web proxy — a known phishing infrastructure pattern.
Understanding the Torzon warrant canary
A cryptographic proof that the market is operating without law enforcement interference.
A warrant canary is a statement published regularly by a service operator asserting that they have not received any secret government demands or legal orders. When Torzon signs this canary with their PGP private key every 72 hours, they prove two things simultaneously: the key has not been compromised, and the publication is current.
The canary includes references to recent news headlines. This prevents an attacker from replaying an old, valid canary — the news references anchor each canary to a specific point in time. Tools like the Blockchain Explorer can provide timestamped data suitable for inclusion.
If the canary stops publishing — or if the PGP signature is invalid — users treat this as a warning signal. Torzon has maintained a clean canary record since September 2022. The 72-hour publication interval is one of the most frequent among active markets, outpacing competitors who publish weekly or monthly.
Canary verification reference
Publication interval
Every 72 hours
Signature algorithm
RSA-4096 (PGP/GPG)
Verification command
gpg --verify canary.asc
Failure signal
Canary older than 72h or invalid signature → treat as compromised; do not log in
"The warrant canary remains the only publicly auditable proof that a market's key has not changed hands. Combined with anti-phishing codes, it forms the two-factor verification layer for the market itself — not just your account."
— Operational security guidance, Dread community wiki, 2025
For users on Whonix or Tails OS, GPG is pre-installed. Run the verification in a terminal window before opening Tor Browser. On standard operating systems, GnuPG is a free download. The Access Now Digital Security Lab offers guidance for users unfamiliar with GPG workflows.
Five verified Torzon mirrors — April 2026
All addresses below are confirmed against the current PGP-signed canary. Copy using the button on the right — never type manually.
These links are maintained by this independent portal. We verify against PGP canaries before each update. Links use data-link attributes — the actual .onion addresses load from _links.json at page load. The HTML source never contains a .onion address directly, preventing cached phishing copies.
What to do if you suspect you entered a phishing page
Act fast. The window to limit damage is usually under 30 minutes.
Do not deposit anything further. If you have already entered credentials on a page that doesn't display your anti-phishing code, treat that username and password as compromised. Do not use them on any other service.
Move funds immediately. If you have a balance on the real Torzon account and believe your credentials were stolen, log in via a verified link (use the addresses above), change your password, withdraw your balance to a fresh wallet address, and enable 2FA if not already active.
Generate new cryptocurrency addresses. Any BTC or XMR address you used on the phishing page should be treated as exposed. Generate fresh addresses in a clean wallet. The CryptoNote Protocol that underlies Monero makes address reuse inadvisable regardless — each transaction to the same address can be linked in chain analysis.
Check for malware. Sophisticated phishing pages deliver browser exploits via JavaScript. If you had Tor Browser's security level below "Safest", run a system scan. On Qubes OS, dispose of the compromised VM entirely and create a new one. On standard systems, consider a full reinstall if you suspect code execution occurred.
Report the phishing address. Document the full .onion address you visited. Post it on the Dread marketplace forum so the community can add it to filter lists. Users running Briar Messenger or Element Chat in darknet privacy communities can alert others quickly.
Wipe your browser session. Delete all Tor Browser data and start a new identity. For maximum isolation, Whonix users should snapshot and restore to a clean state. The session data in Tor Browser contains circuit information that could theoretically be used for timing analysis if the phishing operator also controls exit nodes.
Activate the anti-phishing code on your new session. Once you are certain you are on the real Torzon market — verified via canary, PGP signature, and full address comparison — set a new anti-phishing code immediately. Make it something unrelated to anything you've used before. Update your access procedure to include verification as the first step every single time.
Community-maintained tools that support the verification workflow.
| Tool |
Purpose |
Link |
| Tor Browser |
The only browser for .onion access. Bundles GPG-verifiable signatures on releases. |
torproject.org |
| Whonix OS |
OS that routes all traffic through Tor by design. Eliminates IP leak risk at the system level. |
whonix.org |
| Qubes OS |
Compartmentalised OS; runs Whonix as a VM. Ideal for high-risk sessions. |
qubes-os.org |
| Privacy Guides |
Community-curated index of privacy tools; covers browser hardening and GPG setup. |
privacyguides.org |
| CVE Details |
Database of known browser exploits. Check if your Tor Browser version has outstanding CVEs. |
cvedetails.com |
| Startpage |
Privacy-respecting search engine. Use for research, not for finding .onion links. |
startpage.com |
| Jitsi Meet |
End-to-end encrypted video. Useful for secure communication with vendors or support. |
jitsi.org |
| Internet Archive |
Use for retrieving archived copies of PGP key publications and historical canaries. |
archive.org |
| Access Now |
Digital security helpline. Free assistance for users targeted by phishing or surveillance. |
accessnow.org |
Ready to connect to the real Torzon?
You have the verification process. Use the addresses above, check the canary, set your anti-phishing code on first login. That is the complete protocol.